With the planet going wireless in almost every sphere, Security concerns raise very often. Hackers are constantly trying to achieve access to Wi-Fi networks that are not secured or have some weaknesses. There are many reasons why you would wish have the WiFi protect. Some of the reasons among them going to be embrace higher privacy, reduced net bills and quicker internet speeds. This post contains few easy techniques you’ll be able to use to have the WiFi network as secured as possible.

Protect your Wireless Network
1. Encrypt (Password protect) your Wi-Fi Network: when you use a Wi-Fi network for accessing the web, every bit of information you send and receive will be easily snooped with the proper set of tools. Packet sniffers are very easy to use, even for beginners. This means that a hacker can not only see which websites you are accessing but also get the login details. Encryption basically involves scrambling the data that is send and received, while using a wireless network. This means that even if a hacker intercepts your data transmission, it will be quite difficult to exploit the information.
There are 2 encryption standards that you will use: WEP (Wired Equivalent Privacy) and WPA (Wireless Protected Access). WEP is the older standard of encryption and currently can be bypassed in minutes. WPA is relatively newer however it still has security holes. AirCrack and coWPAtty are 2 free tools that permit anyone to simply crack WEP and WPA encoding using bruteforce technique. WPA2 is the latest standard and is recommended for use, if you wish the very best level of protection for your wireless network. The encoding keys used change each time a device accesses the network making WPA more difficult to hack.
Importantly: Use a strong encryption key. Make sure that it is longer than 10 characters and contains a mixture of capital and small letters, numbers and symbols. Do not use common words, names and dates that people can guess. For best practice, Take a sentence and turn it into a password.
The sentence can be anything personal or something you will remember easily. Take the words from the sentence, abbreviate it and combine in unique form of a password. Here are couple examples.
WOO!iqsi16 = Woohoo! I quit smoking in 2016!
PPumb@tgs = Please pick up more beer at the grocery store.
Tb?ontb?titq = to be? Or not to be? This is the question.
Also you can use common substitutions like: “$” for “s”, “@” for “a,” “1” for “l”, 0 for o (zero for letter o) and so on. And again: Do not use common words, names and dates that people can guess!

2. Replace default passwords on your router. The biggest mistake most users make is not changing default passwords on their routers. Default passwords are available for public throughout manufacturer’s websites and databases. This allows hacktivists to change the security settings of your router according to their desires. Using a strong password for your router ensures that hackers cannot modify your network’s security settings.
3. Change default SSID
Your network’s SSID or Service Set Identifier is the name of your wireless network. Usually, the SSID contains the name of the router’s along with the model number. Changing it to not display this information prevents you from giving additional information.
4. Don’t broadcast your SSID
Hiding SSID prevents unsophisticated and inexperienced hackers and WLAN intruders from finding that your network exists. hiding your SSID is very easy and the option to do it is typically below basic wireless settings on your router’s settings page. However, it’s important to notice that some devices, as well as those running newer versions of Windows or other OS, can show all the networks, although they can’t determine its name. Moreover, your network can still contain the SSID in information if the tools like inSSIDer, Kismet and Commview for WiFi Is used.
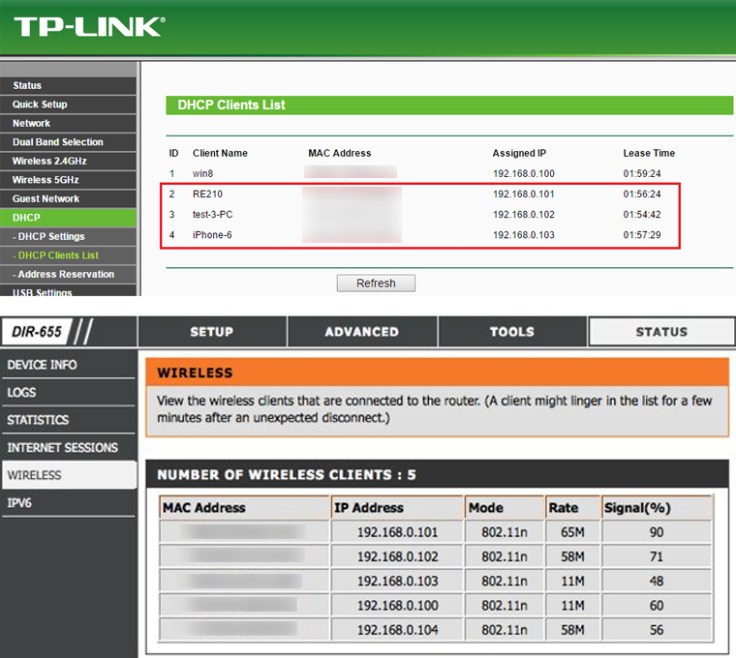
5. See Connected Devices List: all new router will have a page that displays the list of each device that’s connected to the network (Router). You must check this page at regular intervals to make sure that unknown devices aren’t connected to your network. If you see an unknown device, somebody has broken to your network. you can attempt AirSnare, a free utility that scans your network for unknown / unexpected mac addresses and also looks into DHCP requests.
6. Disable Guest networking: while most routers will have guest networking disabled by default, it always a good idea to double check that you did not activate it accidentally. Guest networking still permits others to access your network.
7. Enable mac address based filtering: Media Access Control or mac address identifies every device connected to your network. mac address is an alphanumerical key separated by colons that is unic for each device. Enabling mac address based filtering permits only devices having particular mac addresses to access your network. You need to enter the mac address of each device you would like to allow to connect to your network on your router’s settings page. This prevents unknown devices to connect to your network even if password is known. To find the MAC address of your computer, open command prompt (cmd) and execute “ipconfig /all”.

8. Turn the Firewall On: A “firewall” is designed to protect computers from harmful intrusions and can be hardware-based or software-based. Wireless routers generally contain built-in firewalls, but are sometimes shipped with the firewall turned off. Be sure to check that the firewall is turned on.
importantly When not using your internet network, turn it off: This is self-explanatory. If you are not using your network, turning it off don’t give extra time to hackers to try and hack into your WiFi

